Hundreds of millions of devices, especially Android smartphones and tablets, using Qualcomm chipsets, are vulnerable to a new set of potentially serious vulnerabilities.
According to a report cybersecurity firm CheckPoint shared with The Hacker News, the flaws could allow attackers to steal sensitive data stored in a secure area that is otherwise supposed to be the most protected part of a mobile device.
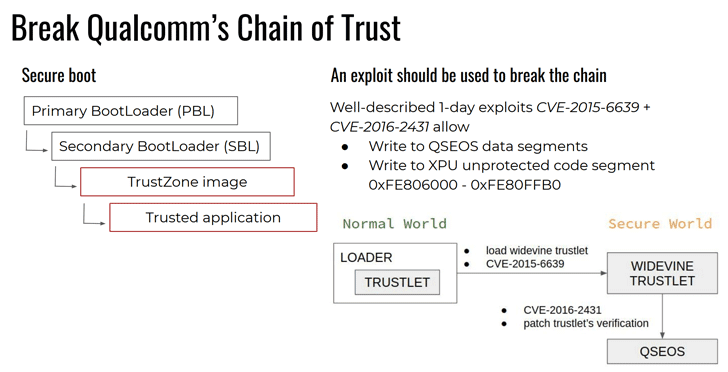
The vulnerabilities reside in Qualcomm’s Secure Execution Environment (QSEE), an implementation of Trusted Execution Environment (TEE) based on ARM TrustZone technology.
Also known as Qualcomm’s Secure World, QSEE is a hardware-isolated secure area on the main processor that aims to protect sensitive information and provides a separate secure environment (REE) for executing Trusted Applications.
Along with other personal information, QSEE usually contains private encryption keys, passwords, credit, and debit card credentials.
Since it is based on the principle of least privilege, Normal World system modules like drivers and applications can not access protected areas unless necessary—even when they have root permissions.
“In a 4-month research project, we succeeded in reverse Qualcomm’s Secure World operating system and leveraged the fuzzing technique to expose the hole,” researchers told The Hacker News.
“We implemented a custom-made fuzzing tool, which tested trusted code on Samsung, LG, Motorola devices,” which allowed researchers to find four vulnerabilities in trusted code implemented by Samsung, one in Motorola and one in LG.
- dxhdcp2 (LVE-SMP-190005)
- sec_store (SVE-2019-13952)
- authnr (SVE-2019-13949)
- esecomm (SVE-2019-13950)
- kmota (CVE-2019-10574)
- tzpr25 (acknowledged by Samsung)
- prov (Motorola is working on a fix)
According to researchers, the reported vulnerabilities in the secure components of Qualcomm could allow an attacker to:
- execute trusted apps in the Normal World (Android OS),
- load patched trusted app into the Secure World (QSEE),
- bypassing Qualcomm’s Chain Of Trust,
- adapt the trusted app for running on a device of another manufacturer,
- and more.
“An interesting fact is that we can load trustlets from another device as well. All we need to do is replace the hash table, signature, and certificate chain in the .mdt file of the trustlet with those extracted from a device manufacturer’s trustlet,” researchers said.
In short, a vulnerability in TEE component leaves devices vulnerable to a wide range of security threats, including the leakage of protected data, device rooting, bootloader unlocking, and execution of undetectable APT.
The vulnerabilities also affect a wide range of smartphone and IoT devices that use the QSEE component to secure users’ sensitive information.
Check Point Research responsibly disclosed its findings to all affected vendors, out of which Samsung, Qualcomm, and LG have already released a patch update for these QSEE vulnerabilities.












![Hotstar Premium Cookies 2019 [*100% Working & Daily Updated*] Hotstar Premium Cookies 2019 [*100% Working & Daily Updated*]](https://tahav.com/wp-content/uploads/2019/11/Hotstar-Premium-Cookies-Free-100x70.jpg)



